On this page
Security Certifications #

SOC 2 Type II
ClearCo is a SOC 2 Type II certified company and completes this audit on an annual basis.
GDPR & CCPA Compliance #
About ClearCo and GDPR compliance >
About ClearCo and CCPA compliance >
Security Features #
SSO
Seamlessly integrate into Okta, OneLogin, Azure AD, Ping Identity or any SAML 2.0 or Active Directory connection.
Two-Factor Authentication
Clients can enable this for all of their users and choose between getting an email, text message or using an app based authenticator.
Identity Provider
ClearCo can act as your identity provider for all of your SSO applications, giving you a single place to disable access when you offboard an employee.
Account Lockout
All user accounts have this protection enabled by default.
Brute Force Mitigation
ClearCo has rate limiting in place on our login page and APIs to prevent this type of attack.
Password Policy
Customers can define their own password complexity policies within the system.
Custom Session Timeouts
ClearCo allows clients to set their own session timeout policy.
Encryption #
SSL Everywhere
Customer data is always encrypted in transit. No insecure requests are allowed.
Sensitive Data Encrypted at Rest
Sensitive PII and other sensitive data is encrypted at rest using AES 256.
Key Management
ClearCo manages customer encryption keys. No encryption keys are ever allowed in the ClearCo codebase.
Database Data Encrypted on Disk
All database servers data drives are encrypted.
Infrastructure & Network Security #
Cloud Platform
ClearCo is a cloud-native, multi-tenancy SaaS Human Capital Management software platform hosted within AWS.
Physical Security
ClearCo offices are secured against unauthorized physical access and procedures for managing visitors are also implemented. The services computing infrastructure is entirely run in the cloud and all services are hosted and managed within Amazon Web Services (AWS), a secure cloud services platform. AWS’ physical infrastructure has been subject to examination under various frameworks and reporting standards, including: ISO 27001, SOC 1/SOC 2/SSAE 18/ISAE 3402, PCI Level 1, FISMA Moderate and Sarbanes-Oxley.
Logical Access Control
ClearCo has implemented role-based security to limit and control access within the ClearCo software platform and any system that houses customer or confidential data. Employees are granted logical and physical access to these systems based on documented approvals by appropriate management personnel. User access is reviewed on a rolling basis or at a minimum annually.
Intrusion Detection & Prevention
ClearCo's infrastructure is monitored in real-time leveraging an IDS. Any alerts are reviewed by our 3rd party SOC and internal security team that’s available 24/7/365.
Uptime Monitoring
All ClearCo services are monitored internally and externally.
Disaster Recovery #
High Availability
The system is an n-tier architecture, a design that is the same across all ClearCo products. ClearCo's infrastructure utilizes several databases and database clusters to allow for high availability and scalability. We also utilize 4 availability zones within AWS to reinforce our commitment of high availability to our customers.
Disaster Recovery Backups to Different Geographic Regions
All databases are backed up to remote regions on a daily basis. All databases run several real-time replicas so that no single database failure can interrupt service or cause data loss. Server configurations and files are also backed up to separate regions.
Business Continuity & Tabletop Exercises
ClearCo has distinct business continuity and disaster recovery plans in place and runs tabletop exercises on an annual basis to ensure all key stakeholders are familiar with the actions that should be followed if such a qualifying event were to take place. These policies are reviewed and updated annually.
Application Security #
Dedicated Team for Application Security
ClearCo has a dedicated application security team that is constantly adding security features, looking for vulnerabilities, and improving the secure posture of the ClearCo platform.
2+ Penetration Tests Per Year
ClearCo conducts 2+ penetration tests per year.
Quarterly Red Team Vulnerability
Every quarter, ClearCo conducts Red Team vulnerability testing and remediation.
System & Application Patching
System & Application Patching is ongoing and immediate should a critical vulnerability be identified.
OWASP Top 10
ClearCo's developers and Application Security team are trained to mitigate the OWASP Top 10 vulnerabilities.
Rapid7 Vulnerability Scanning
Ongoing weekly Rapid7 Vulnerability Scanning.
Corporate Security #
Background Checks
ClearCo does employment verification and background checks, which include financial and/or criminal checks dependent on the position, on all new hires before they start with the company. Failure to pass these will result in their offer of employment being rescinded.
Employee Onboarding and Offboarding
• Asset Management
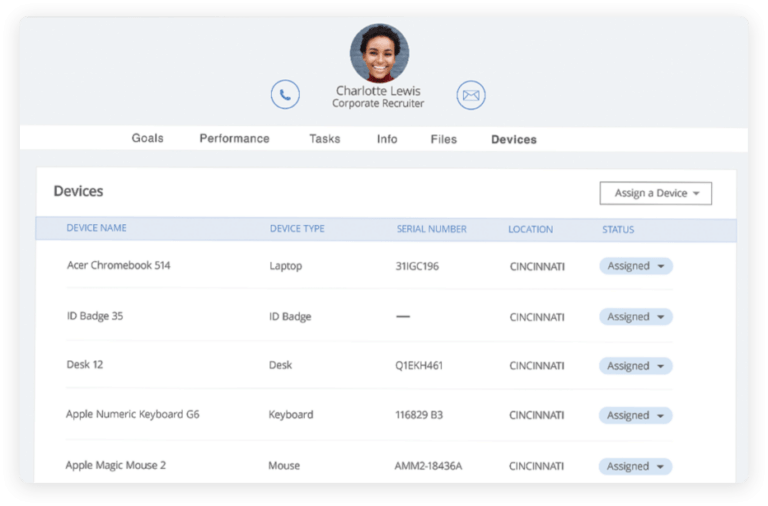
learCo uses our own World of Work Asset Management tool to track all employee assets such as laptops, phones, and much more.
• Identity Provider
ClearCo uses our own World of Work Identity Provider service so that employee accounts can be provisioned and de-provisioned quickly.
Security Training
All new hires undergo security training before getting access to the ClearCo system. All employees complete security training annually.
2FA Everywhere
ClearCo implements 2FA for all critical systems and any other systems that support this.
Endpoint Protection
All laptops and servers have these agents installed to protect against malware and ransomware.
Third Party Vendor Management
All third party vendors undergo a security review that consists of reviewing relevant SOC 2, ISO27001, or supporting security documentation.
